Studybud.in leaky AWS bucket
By Ronak Gothi
How we made an ungrateful Studybud.in to pull up their sleeves and fix their Leaky AWS Bucket?
We at Acuments have a keen eye on web security. We take particular interest in companies whose business revolve around the community. In this case, they help Students prepare for placements.
On Visiting their site, the following section caught our attention, a broken image link
On Inspecting the broken image, it lead us to the following URL
1
https://d31dojnee3z5un.cloudfront.net/staticfiles/media/img/institute/kiet.png
Wanted to play and discover a vulnerability, I slowly traversed till the root of the CDN to know if I could find something interesting. To my surprise, I could find that the directory listing is enabled.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
<ListBucketResult xmlns="http://s3.amazonaws.com/doc/2006-03-01/">
<Name>studybud-cdn</Name>
<Prefix/>
<Marker/>
<MaxKeys>1000</MaxKeys>
<IsTruncated>true</IsTruncated>
<Contents>
<Key>staticfiles/media/android/img/</Key>
<LastModified>2019-02-07T08:39:43.000Z</LastModified>
<ETag>"d41d8cd98f00b204e9800998ecf8427e"</ETag>
<Size>0</Size>
<Owner>
<ID>
5d7db07078612fd57f02af6b8eb7ecae983dd037b4b4110a82f4366a7210116c
</ID>
</Owner>
<StorageClass>STANDARD</StorageClass>
</Contents>
</ListBucketResult>
Now that We have the S3 bucket name studybud-cdn, We now wanted to see if the bucket has necessary permissions set. We had a gut feeling that it's insecure.
Voila!!!

For better readability
1
2
Ronaks-MacBook-Pro:S3Scanner ronak$ python ./s3scanner.py studybud-cdn
2019-05-07 16:15:54 [found] : studybud-cdn | Unknown Size - timeout | ACLs: {'authUsers': [], 'allUsers': ['READ', 'WRITE', 'FULL_CONTROL', 'READ_ACP', 'WRITE_ACP']}
We could see that the bucket has FULL_CONTROL permission give for allUsers. This is the worst possible way to set your AWS bucket.
For the successful completion of POC, we would need to
- Create files in their bucket
- Move files in their bucket
- Delete files in their bucket
1
2
3
4
Ronaks-MacBook-Pro:S3Scanner ronak$ aws s3 mv ~/Desktop/hacked.png s3://studybud-cdn/staticfiles/media/img/
move: ../../../Desktop/hacked.png to s3://studybud-cdn/staticfiles/media/img/hacked.png
Ronaks-MacBook-Pro:S3Scanner ronak$ aws s3 rm s3://studybud-cdn/staticfiles/media/img/hacked.png
delete: s3://studybud-cdn/staticfiles/media/img/hacked.png
Now as a good Samaritan, we informed their Management.
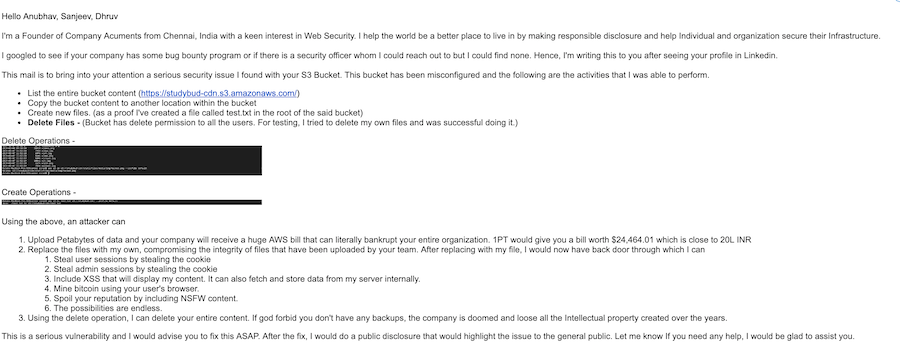
Within 24 hours, they pulled up their sleeves and the bucket now seem to have limited permission for allUsers
1
2
Ronaks-MacBook-Pro:S3Scanner ronak$ python ./s3scanner.py studybud-cdn
2019-05-08 18:57:35 [found] : studybud-cdn | Unknown Size - timeout | ACLs: {'authUsers': [], 'allUsers': ['READ', 'READ_ACP', 'READ', 'READ_ACP']}
Sounds good right? Should be grateful? Yes, they should be, we helped them safeguard their infrastructure. But till now there was not even an acknowledgement. No thankyou email.
Don't be like them. If you dont have budget to pay them, treat your informers well with a coffee maybe ?